You can secure your secrets like passwords and database connection strings by saving them in Azure Key Vault. Azure Key Vault is a cloud service offered by Microsoft to securely store cryptographic keys, certificates, and secrets.
Following Azure resources are required handy to get access to secret value stored in Key Vault using POSTMAN-
>>Tenant Id
>>Service Principal: Client id and Client secret
>>Key Vault URI & Key Vault Secret Name
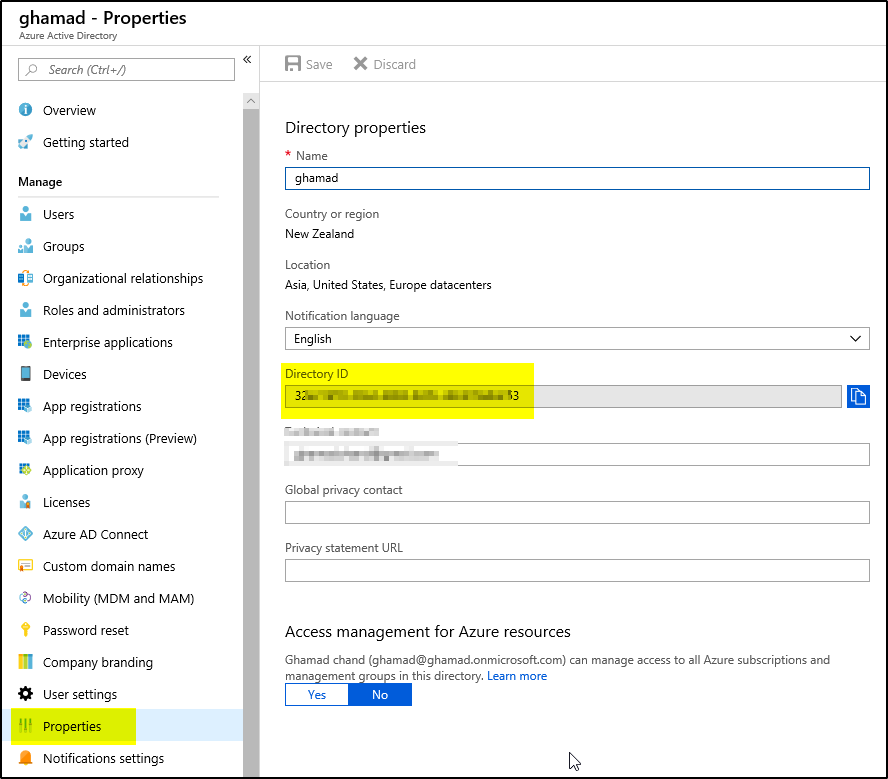
Find Tenant ID
1. Login to https://portal.azure.com, Go to Azure Active Directory–>Properties and copy Directory ID value, it is the tenant id:
Create Key Vault and Secret
2. This article assumes that you already have created Key Vault and a Secret in it. If not, then you can create one using this link.
Create Service Principal and Assign Access
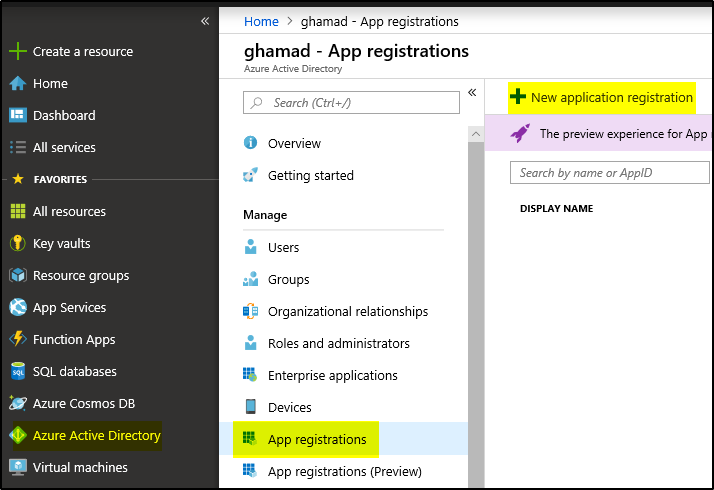
3. Now create a Service Principal. Login to https://portal.azure.com
4.Go to Azure Active Directory–>App Registrations –>+New application registration
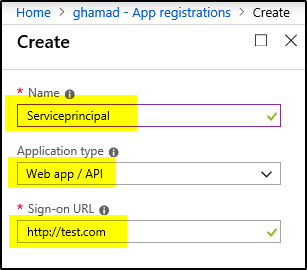
5. Provide Service Principal name, Application Type and Sign-On URL (it could be any dummy URL) and then click Create:
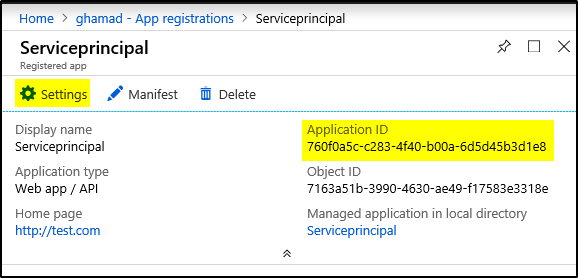
6. Copy the Application ID (Client Id) and click on Settings:
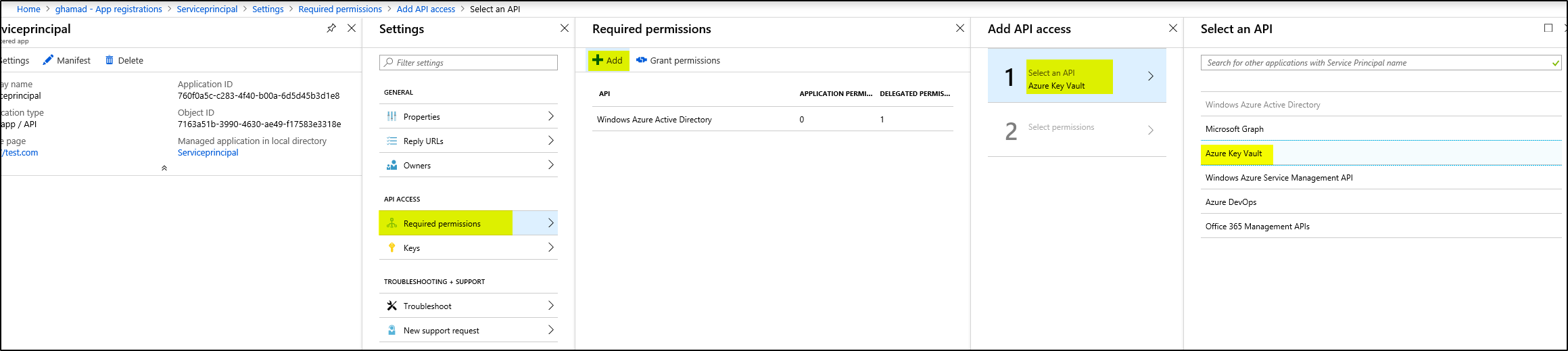
7. Then click on Required permissions–>+Add–>Select an API–>select Azure Key Vault and click Select:
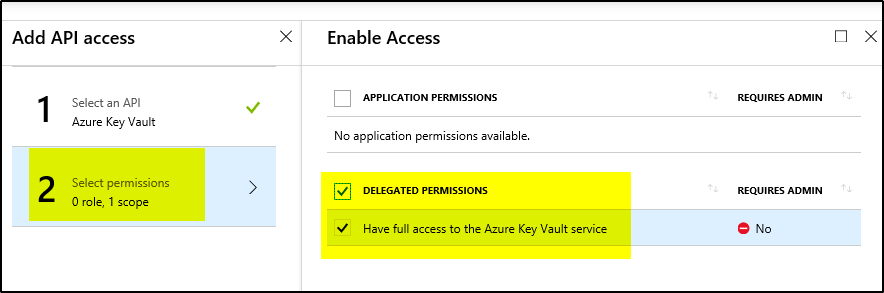
8. Then click Select permissions –> Delegated permissions and Done
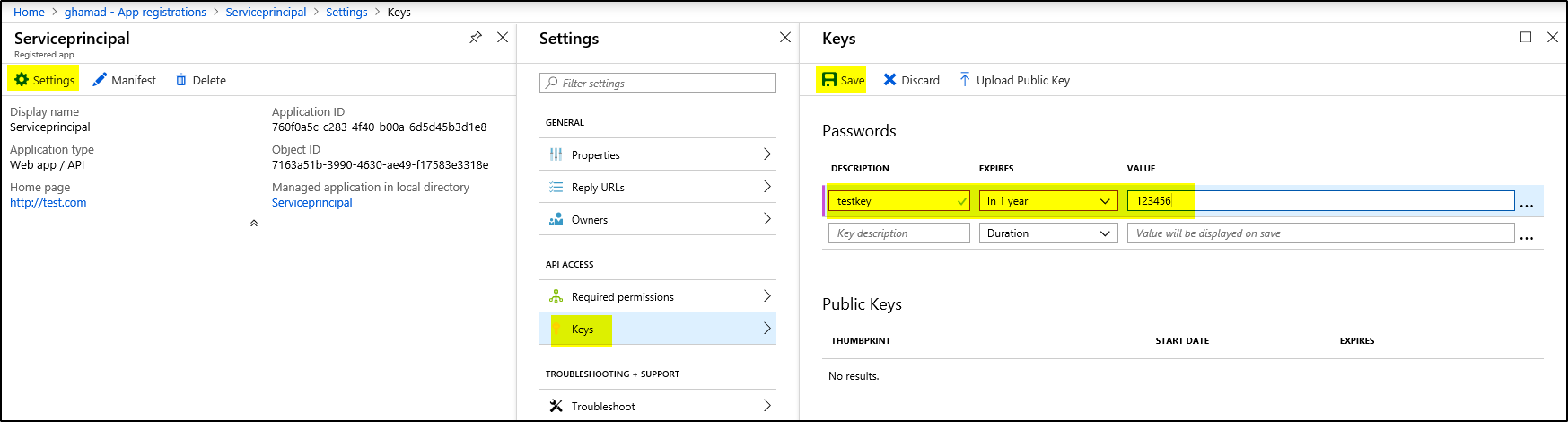
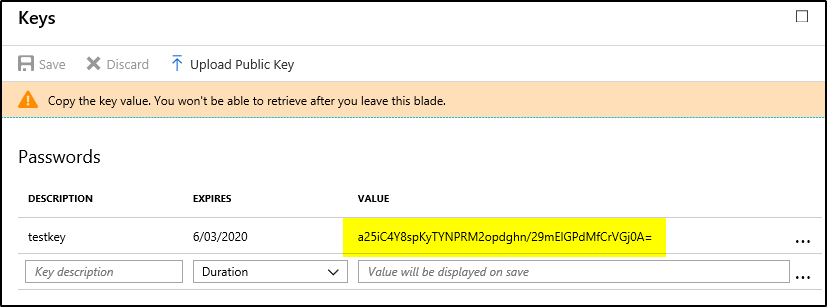
9. Now click on Keys –> provide key name , duration and password and click Save. This will provide key value which you should copy before closing the screen. It is Client_secret.
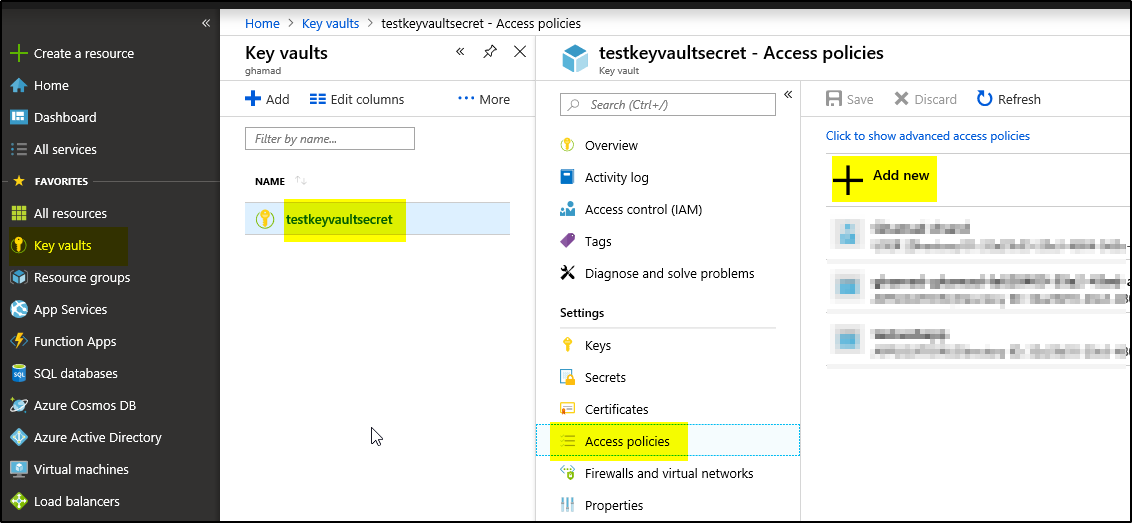
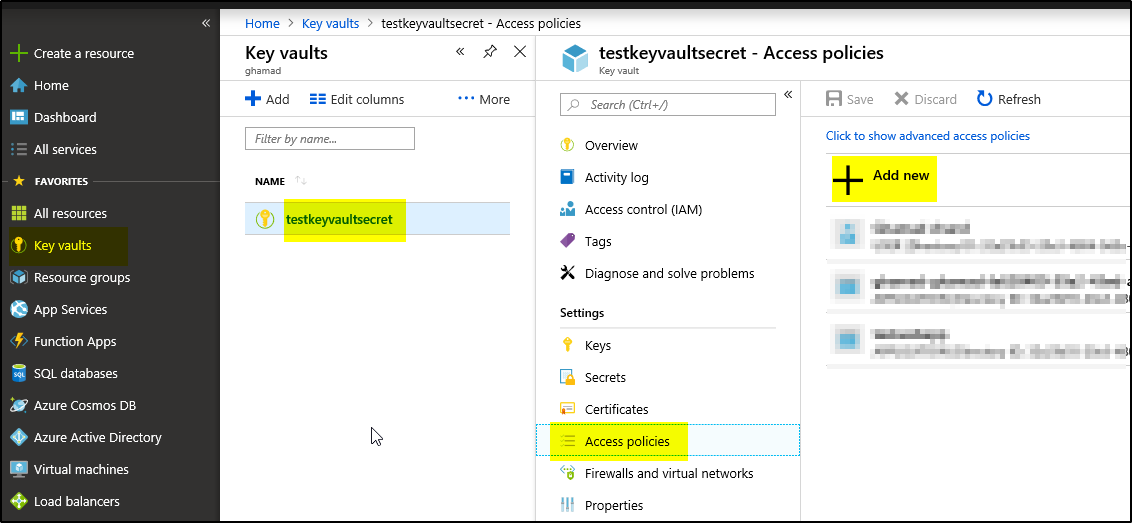
 10. Go to Key vaults –> Select the keyvault–>Access policies –> + Add new
10. Go to Key vaults –> Select the keyvault–>Access policies –> + Add new
11. Select “Secret Management”, select the Service principal and the click OK and then Save.
REST API with POSTMAN
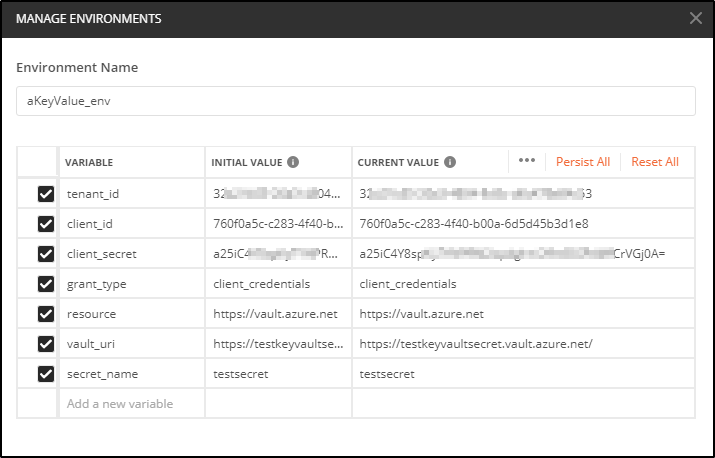
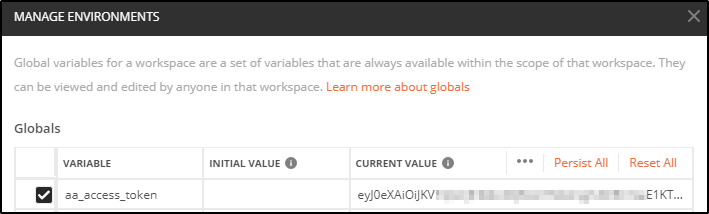
12. Now Open POSTMAN and create a Collection (aKeyVault) and add environment variables with values which we noted down earlier. Also add a Global variable “aa_access_token”:
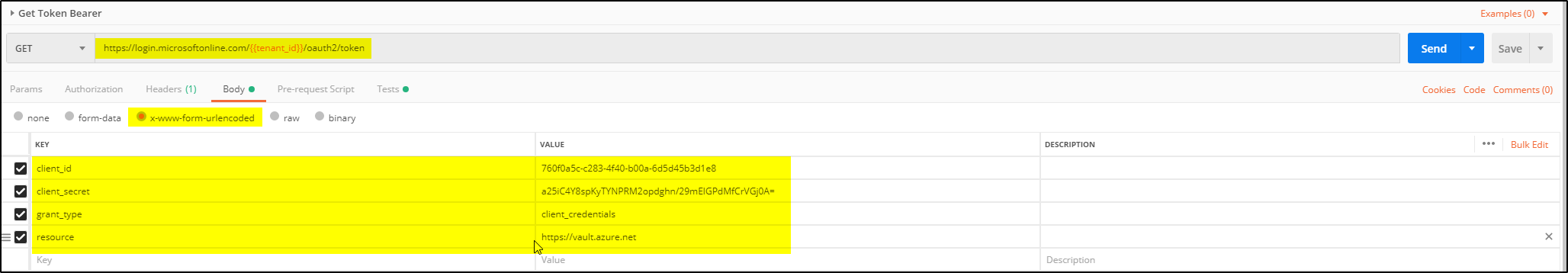
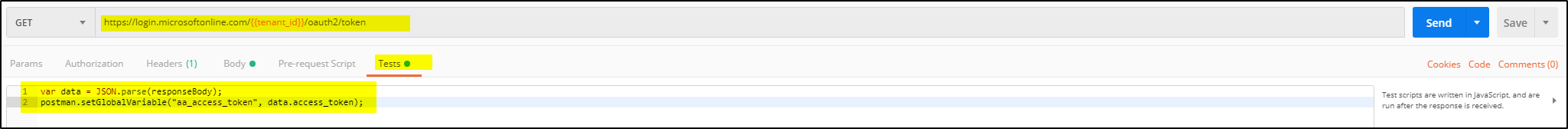
13. Add Get Token Bearer Request to this Collection:
14. On Click Send, it will populate the global variable “aa_access_token” with token value.
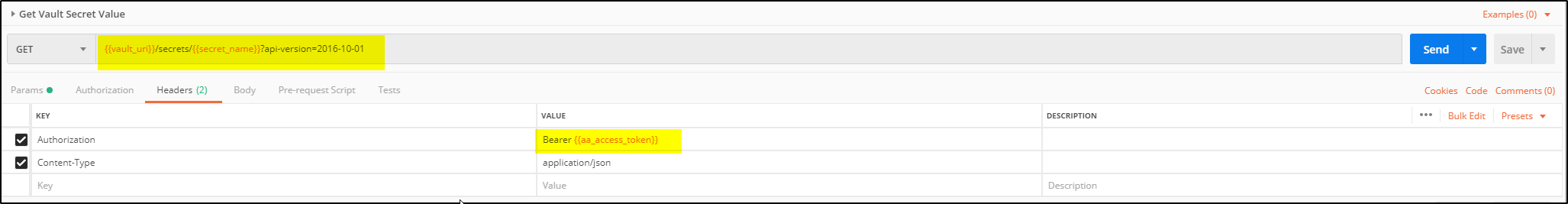
15. Now add another Get request to this collection (Get Vault Secret Value):
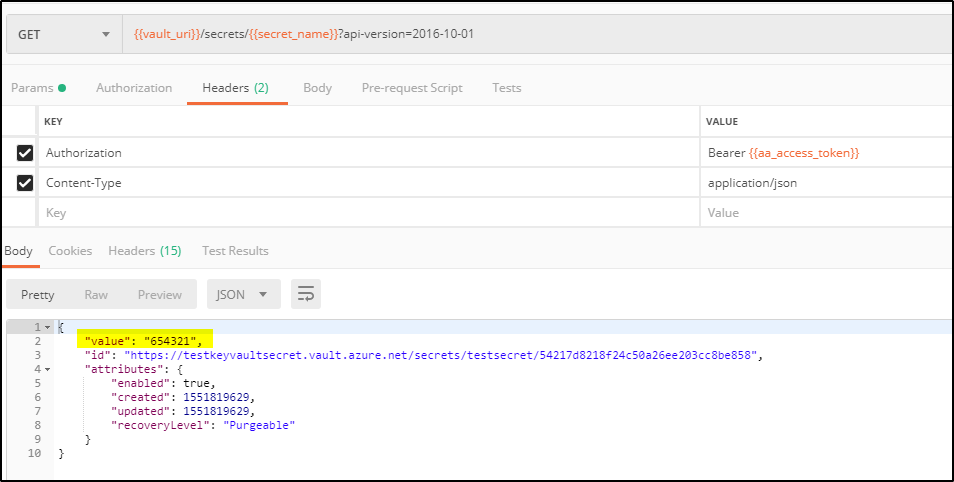
16. Clicking on Send it will show the Secret value as below: