If you are using AWS SSO then you can designate which users and groups have SSO access to AWS accounts in your AWS organization. You can also manage permission sets to control the users’ level of access to these AWS accounts.
The user portal offers a single place to access all their assigned AWS accounts and applications. To access the AWS account or Applications, user logs into user portal.
SSO user gets link to connect to Management console and Command line or programmatic access as shown
Now open Visual Studio. Make sure you have installed extension “AWS Toolkit for Visual Studio”
Go to View Menu –> AWS explorer
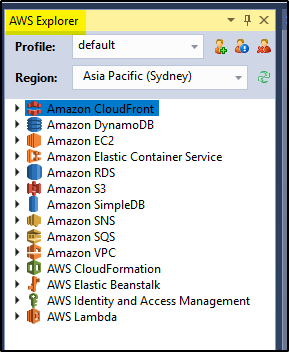 Click on edit profile icon (middle one). Enter the Access Key ID and Secret Access Key values in this pop-up from the above shown Command line or programmatic access screen and Account Number. Click OK.
Click on edit profile icon (middle one). Enter the Access Key ID and Secret Access Key values in this pop-up from the above shown Command line or programmatic access screen and Account Number. Click OK.
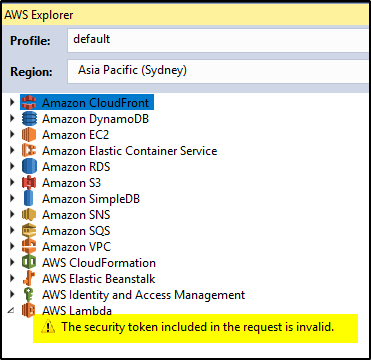
When you try accessing any data, it will throw error “The security token included in the request is invalid“.
This happens because the AWS SSO user is not IAM user. The access to AWS resources is based on ROLE assigned to the user. You have to use “aws_session_token” value to connect. There is no way to provide this information in Visual studio UI.
So work around is to open the file
USERNAME>\.aws\credentialsIt will have entries like below-
[default] aws_access_key_id=ASIARBHKUDWSNNTN64YW aws_secret_access_key=AgoJb3JpZ2luX2VjEMj toolkit_artifact_guid=1b11b01d-43fc-458b-800c-8491a0150f3a
You have to add aws_session_token value as copied from Command line or programmatic access screen.
After the update the entry will look like this-
[default]
aws_access_key_id=ASIARBHKUDWSNNTN64YW
aws_secret_access_key=AgoJb3JpZ2luX2VjEMj
aws_session_token=AgoJb3JpZ2luX2VjEMj//////////wEaDmFwLXNvdXRoZWF
toolkit_artifact_guid=1b11b01d-43fc-458b-800c-8491a0150f3a
Now save the file and restart the Visual Studio. This time the AWS resource will be accessible. There is a catch. The session token will expire after some time depending on the session expiry set for the ROLE in AWS SSO.
Another way is to replace the full content of C:\Users\<your USERNAME>\.aws\credentials by OPTION 2 value from Command line or programmatic access screen. It will look like this
[AWS_FullAccess] aws_access_key_id = ASIAREM6VOLT7 aws_secret_access_key = Zw9Kg57RvzoKZ26uSY0me aws_session_token = AgoJb3JpZ2luX2VjEN7//////////wEaDmFwLXqYx5HpkhRWtm0MQH9CJH4n
Now open the Visual studio and select the profile “AWS_FullAccess” to connect to AWS.